 |
 |
 |
 |
 |
|
|---|---|---|---|---|---|
 |
 |
 |
 |
 |
|
| Braindump2go | Testking | Pass4sure | Actualtests | Others | |
| $99.99 | $124.99 | $125.99 | $189 | $29.99/$49.99 | |
| Up-to-Dated | ✔ | ✖ | ✖ | ✖ | ✖ |
| Real Questions | ✔ | ✖ | ✖ | ✖ | ✖ |
| Error Correction | ✔ | ✖ | ✖ | ✖ | ✖ |
| Printable PDF | ✔ | ✖ | ✖ | ✖ | ✖ |
| Premium VCE | ✔ | ✖ | ✖ | ✖ | ✖ |
| VCE Simulator | ✔ | ✖ | ✖ | ✖ | ✖ |
| One Time Purchase | ✔ | ✖ | ✖ | ✖ | ✖ |
| Instant Download | ✔ | ✖ | ✖ | ✖ | ✖ |
| Unlimited Install | ✔ | ✖ | ✖ | ✖ | ✖ |
| 100% Pass Guarantee | ✔ | ✖ | ✖ | ✖ | ✖ |
| 100% Money Back | ✔ | ✖ | ✖ | ✖ | ✖ |
[February-2021]High Quality Braindump2go 220-1002 Exam PDF and VCE 220-1002 624 Free Share[Q600-Q624]
2021/February Latest Braindump2go 220-1002 Exam Dumps with PDF and VCE Free Updated Today! Following are some new 220-1002 Real Exam Questions!
QUESTION 600
A technician encounters a previously unidentified issue The technician conducts some research, finds a solution, and resolves the issue. According to best practices, which of the following should the technician do so the issue can be addressed if it is encountered again?
A. Inform the immediate supervisor about the findings.
B. Email all the other technicians to explain the problem and resolution.
C. Enter the resolution in the ticket and close it.
D. Add the findings to the knowledge base
Answer: A
QUESTION 601
A user is trying to access a popular email website but Is being redirected to a different website that asks for login credentials. The user calls a technician, who promptly notices a security issue. Which of the following should the technician do to remove the threat from the system?
A. Remove all parameters after the FQDN website address
B. Remove all files from the temporary folder and restart the computer.
C. Remove and reinstall the web browser In safe mode.
D. Remove all lines that are not comments from the hosts file
Answer: A
QUESTION 602
A company recently upgraded its computers from Windows XP SP3 lo Windows 7. Due to budget constraints, the company was not able to purchase newer machines. The computers do not have TPM chips. Out the company would like to secure the information on the local hard disk in case the hard drive is stolen, while being able to access all of its information even if users leave. Which of the following would allow the company to accomplish this task?
A. Encrypted file system
B. BitLocker
C. Secure Boot
D. BIOS password
Answer: B
QUESTION 603
Which of the following would MOST likely be connected to a computer Id provide electricity in case of a blackout?
A. Battery backup
B. Surge suppressor
C. Portable generator
D. Power inverter
Answer: A
QUESTION 604
A special type of ESD-sale vacuum cleaner may be necessary to safely clean large spills of:
A. toner.
B. battery acid.
C. ink.
D. filament
Answer: A
QUESTION 605
A technician just finished using BiteLocker to Go. The technician MOST likely encrypted:
A. A CD-RW disk.
B. the network drive.
C. the internal disk drive.
D. A USB drive
Answer: D
QUESTION 606
A technician is reviewing system updates. Some of the updates address vulnerabilities found in mission-critical servers, and they need to be performed immediately. Which of the following should the technician perform FIRST?
A. Risk analysis
B. Back-out plan
C. Change board
D. Implementation plan
Answer: A
QUESTION 607
Given the following batch file:
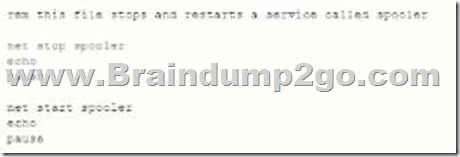
Which of the following describes the purpose of the line beginning with rem?
A. Comment
B. Loop
C. Variable
D. String
Answer: B
QUESTION 608
A technician is setting up a SOHO router for a customer. Per the customer’s requirements, data security is the highest priority. Which of the following provides the MOST security for the network?
A. Set up encryption for wireless
B. Set up port forwarding.
C. Set static IP addresses.
D. Change the default SSID.
Answer: A
QUESTION 609
Which of the following OS types provides a lightweight option for workstations that need an easy-to- use browser-based interface?
A. macOS
B. Windows
C. Linux
D. Chrome
Answer: D
QUESTION 610
The IT department must ensure previously used passwords cannot be reused when users change their passwords. Which of the following password policies should be enforced to meet this requirement? (Select TWO.)
A. Password complexity
B. Password history
C. Password length
D. Maximum password age
E. Minimum password age
F. Lockout threshold
Answer: BE
QUESTION 611
A customer’s computer was turned off overnight, When the customer restarts the computer, an advanced startup menu is displayed.
The startup repair option is unsuccessful and causes the computer to reboot repeatly untill the advanced startup screen reappears. Which of the following should a technician attempt FIRST?
A. Go back to the previous build.
B. Refresh the PC.
C. Run System Restore.
D. Perform System image Recovery.
E. Reset the PC.
Answer: C
QUESTION 612
An end user who travels frequently receives a lot of span and ransomware emails. The user has asked a technician to help ensure the data is secure and application regularly without the need for equirpment. Which of the following would be the BEST method?
A. Account recovery
B. Local restore point
C. Cloud storage
D. File-level encryption
Answer: C
QUESTION 613
Joe, a user, notices someone use his computer while he was on break, Joe s browser history reveals searches for websites he did not visit. The local print also has document in the output tray with someone else’s PII. Which of the following steps should Joe take to prevent unauthorized access of his account.
A. Lock the desktop while he is away
B. Change his password
C. Implement login time restriction
D. Change the default administrator password
Answer: B
QUESTION 614
A technician is setting up network adapter settings on Windows clients that have static IP address assignments. The technician has more than 100 workstation to complete and wants to automate the process. The requirements for the adapter settings are as follows:
– They must utilize a command line utility
– The technician has no access to Group Policy
– All work tation should have an IP address assigned by the DHCP.
Which of the following steps should the technician perform to meet these requirements?
A. Use the ipconfig/release and ipconfig /renev command to have the workstation contact the DHCP for a new lease. Place these two commands in a ,bat file to execute on all systems.
B. Use the petsh command to reset the workstation adapter. Then use the ipconfig /renew command to use DHCP for a new lease. Place these two commands in a ,bat file to execute on all systems.
C. Use the net use command to view active connection on the network. Then use the ipconf /renew command to use DHCP for a new lease. Place these two commands in a ,bat file to execute on all systems.
D. Use the netstat command to find connections on the workstation adapter. Then use the ipconf /renew command to use DHCP for a new lease. Place these two commands in a .bat file to execute on all systems.
Answer: B
QUESTION 615
A technician is able to connect to a website: however, the technician receives the following error, when alternating to access a different website: Page cannot be displayed. Which of the following command line tools would be BEST to identify the root cause of the connection problem?
A. ipconfig
B. tracert
C. nslookup
D. netstat
E. ping
Answer: C
QUESTION 616
Which of the following types filesystems is in use when data is endiphered on a disk using a key?
A. exFAT
B. HFS
C. FAT
D. EFS
Answer: D
QUESTION 617
Which of the following is used with WPA2 to authenticate wireless clients?
A. TACACS
B. LDAP
C. RADIUS
D. MDM
Answer: C
QUESTION 618
A user can no longer edit files on the company shared drive. The user previously used has access to these files. A technician verifies the user can view the folders but cannot open any subfolders or folders. Which of the following must happen to fix this issue?
A. The user should ask the file owners for permission and then let the technician know.
B. The technician needs to update the local Be permissions to include read write. and modify access
C. The technician must update the server permissions to include read, write and modify access.
D. The technician’s update supervisor must approve the access and update the file explorer permission to read, write, and modify access.
Answer: A
QUESTION 619
Which of the following are best practices to avoid ESD-related damage when handling internal computer components? (Select TWO.)
A. Ground onself before touching component
B. Avoid exposing components to source of RFI.
C. Maintain cool and dry air in the work environment.
D. Handle cards by their edges to avoid contacting ICs.
E. Wear adequate eye protection at all times.
F. Ensure hardware is plugged into a grounded outlet.
Answer: AD
QUESTION 620
A technician is implementing a change to a piece of production environment. The change is causing other several other problem to occur. Which of the following should the technician do NEXT?
A. Complete the change to the prod ction environment within the allotted time frame.
B. Attempt to recreate the issues in the QA environment troubleshoot them quickly.
C. Begin following the back-out plan that was outlined in the planning meeting.
D. Complete a risk analysis of the new changes and their potential impact on other systems.
Answer: B
QUESTION 621
A technician is planning a new desktop rollout project for a company. The company wants to donate systems to the library for reuse. The company does not store sensitive material on the desktops, but it does want all the data to be deleted and not easily recoverable. Which of the following methods would be BEST for the technician to perform to prepare the system for donation?
A. Low-level formatting
B. Degaussing
C. Encrypting
D. Drive wiping
Answer: A
QUESTION 622
After a successful phishing attempt on a corporate workstation, the workstation is infected with malware that went undetected by the antivirus. When a technician arrives to investigate the issue, the workstation is no longer in a bootable state. Recovery is not possible, and the operating system has to be reinstalled completely. Which of the following would MOST likely prevent a future infection?
A. Creating regular restore points
B. Educating the user
C. Scanning for viruses frequently
D. Channing to a different antivirus vendor
Answer: B
QUESTION 623
A user is attempting to open Outlook, Outlook seems to have cached some invalid user login information, causing it to fail when trying to connect to Office 365 applications. Which of the following Control Panel applets should a technician use to clear the cached invalid user login information?
A. Network and Sharing Center
B. Sync Center
C. User Account Control
D. Credential manager
Answer: D
QUESTION 624
A technician is setting up a new laptop for a doctor to take to a conference. The laptop contains private health information, and the technician needs to ensure the laptop is protected from unauthorized access in case it us lost or stolen. Which of the following the technician implement the BEST meet this requirement? (Select TWO.)
A. UEFI password
B. Privacy screen protector
C. Login time restrictions
D. User account restrictions
E. Password expiration
F. Full disk encryption
Answer: AE
Resources From:
1.2021 Latest Braindump2go 220-1002 Exam Dumps (PDF & VCE) Free Share:
https://www.braindump2go.com/220-1002.html
2.2021 Latest Braindump2go 220-1002 PDF and 220-1002 VCE Dumps Free Share:
https://drive.google.com/drive/folders/1L-08gjRWfMZvp3WyBb5sTwqtiKr6P3Qn?usp=sharing
3.2021 Free Braindump2go 220-1002 Exam Questions Download:
https://www.braindump2go.com/free-online-pdf/220-1002-PDF-Dumps(610-624).pdf
https://www.braindump2go.com/free-online-pdf/220-1002-VCE-Dumps(593-609).pdf
Free Resources from Braindump2go,We Devoted to Helping You 100% Pass All Exams!
![[December-2020]SY0-601 VCE and PDF Free Download in Braindump2go[Q49-Q70]](https://www.examsforalls.com/wp-content/themes/ribbon-lite/images/nothumb-related.png)